SABnzbd in Autopirate Docker Swarm stack
Skip the setup and get SABnzbd "ElfHosted"!
Want to skip the self-assembly, and have SABnzbd INSTANTLY "Just Work™"?
ElfHosted is an open-source app hosting platform (geek-cookbook-as-a-service), crafted with love by @funkypenguin - get your ElfHosted instance of SABnzbd now!
Warning
This is not a complete recipe - it's a component of the AutoPirate "uber-recipe", but has been split into its own page to reduce complexity.
Introduction
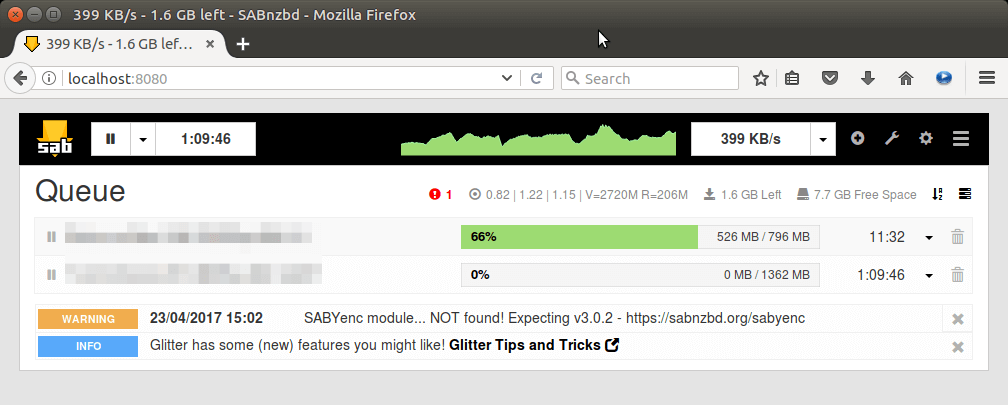
SABnzbd is a workhorse of the stack. It takes .nzb files as input (manually or from other autopirate stack tools), then connects to your chosen Usenet provider, downloads all the individual binaries referenced by the .nzb, and then tests/repairs/combines/uncompresses them all into the final result - media files.
Inclusion into AutoPirate
To include SABnzbd in your AutoPirate stack, include something like the following example in your autopirate.yml docker-compose stack definition file:
Fast-track with premix! 🚀
"Premix" is a git repository which includes necessary docker-compose and env files for all published recipes. This means that you can launch any recipe with just a git pull and a docker stack deploy 👍.
🚀 Update: Premix now includes an ansible playbook, enabling you to deploy an entire stack + recipes, with a single ansible command! (more here)
sabnzbd:
image: lscr.io/linuxserver/sabnzbd:latest
env_file : /var/data/config/autopirate/sabnzbd.env
volumes:
- /var/data/autopirate/sabnzbd:/config
- /var/data/media:/media
networks:
- internal
deploy:
labels:
# traefik
- traefik.enable=true
- traefik.docker.network=traefik_public
# traefikv1
- traefik.frontend.rule=Host:sabnzbd.example.com
- traefik.port=8080
- traefik.frontend.auth.forward.address=http://traefik-forward-auth:4181
- traefik.frontend.auth.forward.authResponseHeaders=X-Forwarded-User
- traefik.frontend.auth.forward.trustForwardHeader=true
# traefikv2
- "traefik.http.routers.sabnzbd.rule=Host(`sabnzbd.example.com`)"
- "traefik.http.routers.sabnzbd.entrypoints=https"
- "traefik.http.services.sabnzbd.loadbalancer.server.port=8080"
- "traefik.http.routers.sabnzbd.middlewares=forward-auth"
Important Note re hostname validation
(Updated 10 June 2018) : In SABnzbd 2.3.3, hostname verification was added as a mandatory check. SABnzbd will refuse inbound connections which weren't addressed to its own (initially, autodetected) hostname. This presents a problem within Docker Swarm, where container hostnames are random and disposable.
You'll need to edit sabnzbd.ini (only created after your first launch), and replace the value in host_whitelist configuration (it's comma-separated) with the name of your service within the swarm definition, as well as your FQDN as accessed via traefik.
For example, mine simply reads host_whitelist = sabnzbd.funkypenguin.co.nz, sabnzbd
Assemble more tools..
Continue through the list of tools below, adding whichever tools your want to use, and finishing with the end section:
- Headphones
- Heimdall
- Jackett
- Lazy Librarian
- Lidarr
- Mylar
- NZBGet
- NZBHydra
- Ombi
- Prowlarr
- Radarr
- Readarr
- RTorrent
- SABnzbd
- Sonarr
- End (launch the stack)
Chef's notes 📓
-
In many cases, tools will integrate with each other. I.e., Radarr needs to talk to SABnzbd and NZBHydra, Ombi needs to talk to Radarr, etc. Since each tool runs within the stack under its own name, just refer to each tool by name (i.e. "radarr"), and docker swarm will resolve the name to the appropriate container. You can identify the tool-specific port by looking at the docker-compose service definition. ↩
Tip your waiter (sponsor) 👏
Did you receive excellent service? Want to compliment the chef? (..and support development of current and future recipes!) Sponsor me on Github / Ko-Fi / Patreon, or see the contribute page for more (free or paid) ways to say thank you! 👏
Employ your chef (engage) 🤝
Is this too much of a geeky PITA? Do you just want results, stat? I do this for a living - I'm a full-time Kubernetes contractor, providing consulting and engineering expertise to businesses needing short-term, short-notice support in the cloud-native space, including AWS/Azure/GKE, Kubernetes, CI/CD and automation.
Learn more about working with me here.
Flirt with waiter (subscribe) 💌
Want to know now when this recipe gets updated, or when future recipes are added? Subscribe to the RSS feed, or leave your email address below, and we'll keep you updated.